Aurich Lawson | Getty Pictures
A the latest shift by Google to populate the Online with 8 new major-amount domains is prompting concerns that two of the additions could be a boon to on-line scammers who trick individuals into clicking on malicious one-way links.
Frequently abbreviated as TLD, a prime-stage area is the rightmost section of a area name. In the early times of the Web, they aided classify the intent, geographic area, or operator of a given area. The .com TLD, for instance, corresponded to sites run by professional entities, .org was utilised for nonprofit businesses, .web for Web or network entities, .edu for faculties and universities, and so on. There are also country codes, this sort of as .united kingdom for the United Kingdom, .ng for Nigeria, and .fj for Fiji. A person of the earliest Net communities, The Very well, was reachable at www.properly.sf.ca.us.
Since then, the corporations governing World-wide-web domains have rolled out 1000’s of new TLDs. Two months ago, Google included eight new TLDs to the World wide web, bringing the full range of TLDs to 1,480, in accordance to the Web Assigned Figures Authority, the governing overall body that oversees the DNS Root, IP addressing, and other Net protocol resources.
Two of Google’s new TLDs—.zip and .mov—have sparked scorn in some safety circles. While Google marketers say the aim is to designate “tying items jointly or relocating truly fast” and “moving pics and what ever moves you,” respectively, these suffixes are by now greatly employed to designate one thing completely distinctive. Especially, .zip is an extension employed in archive documents that use a compression format acknowledged as zip. The structure .mov, in the meantime, appears at the end of video clip data files, ordinarily when they have been made in Apple’s QuickTime structure.
Many security practitioners are warning that these two TLDs will result in confusion when they’re exhibited in email messages, on social media, and somewhere else. The explanation is that a lot of internet sites and computer software quickly convert strings like “arstechnica.com” or “mastodon.social” into a URL that, when clicked, leads a consumer to the corresponding domain. The get worried is that email messages and social media posts that refer to a file this kind of as set up.zip or trip.mov will mechanically transform them into clickable links—and that scammers will seize on the ambiguity.
“Threat actors can effortlessly sign up domain names that are probably to be applied by other people to casually refer to file names,” Randy Pargman, director of menace detection at safety company Proofpoint, wrote in an electronic mail. “They can then use individuals discussions that the danger actor didn’t even have to initiate (or take part in) to lure persons into clicking and downloading destructive content material.”
Undoing decades of anti-phishing and anti-deception awareness
A scammer with manage of the domain pictures.zip, for occasion, could exploit the many years-extended pattern of persons archiving a established of visuals inside of a zip file and then sharing them in an electronic mail or on social media. Fairly than rendering pics.zip as plaintext, which would have occurred right before Google’s shift, lots of websites and applications are now converting them to a clickable area. A user who thinks they are accessing a photograph archive from another person they know could as a substitute be taken to a web-site established by scammers.
Scammers “could simply established it up to provide a zip file download any time any person visits the web site and include things like any content material they want in the zip file, these as malware,” said Pargman.
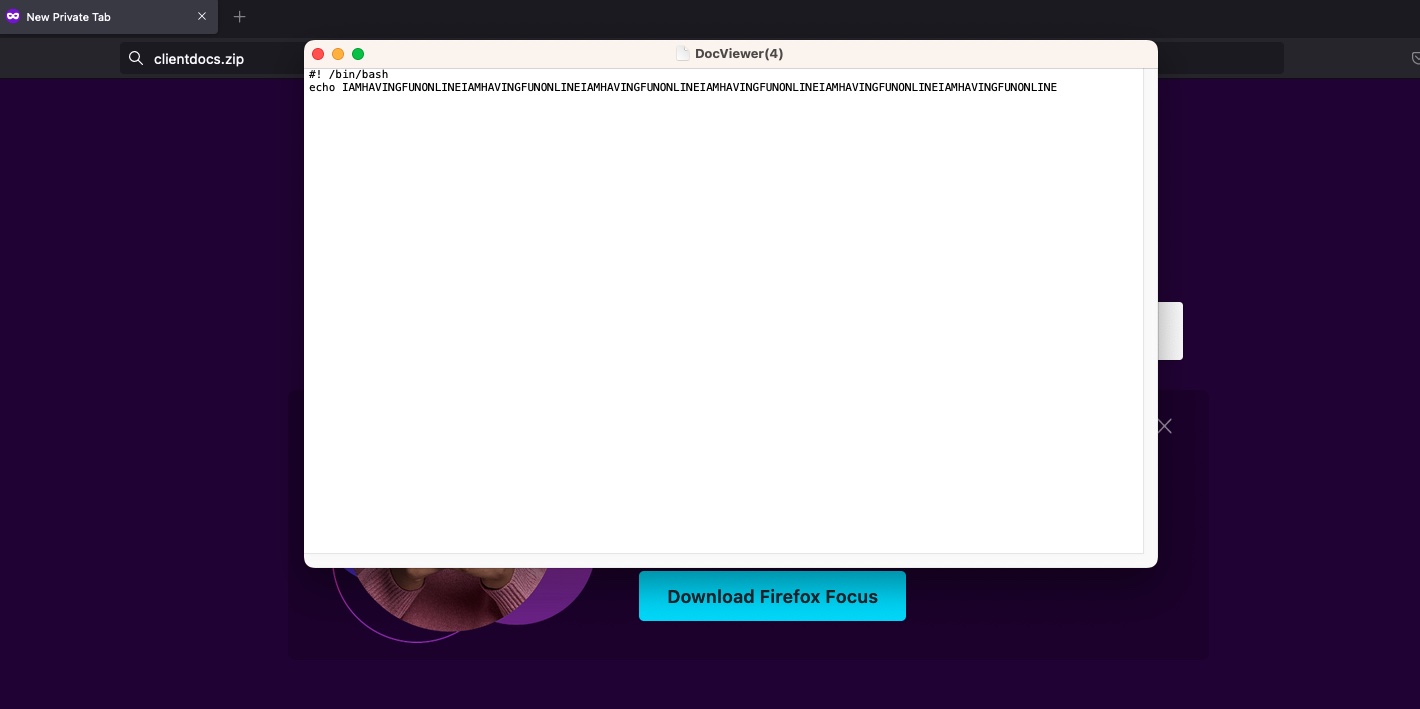
Many newly produced web-sites reveal what this sleight of hand might seem like. Among the them are set up.zip and steaminstaller.zip, which use domain names that frequently refer to naming conventions for installer information. Especially poignant is clientdocs.zip, a site that routinely downloads a bash script that reads:
#! /bin/bash echo IAMHAVINGFUNONLINEIAMHAVINGFUNONLINEIAMHAVINGFUNONLINEIAMHAVINGFUNONLINEIAMHAVINGFUNONLINEIAMHAVINGFUNONLINE
It is not hard to imagine threat actors employing this procedure in ways that aren’t nearly as comical.
“The edge for the menace actor is that they did not even have to send the messages to entice possible victims to click on on the link—they just had to register the domain, set up the web site to serve malicious written content, and passively wait for people today to accidentally create links to their written content,” Pargman wrote. “The hyperlinks appear substantially additional dependable for the reason that they appear in the context of messages or posts from a dependable sender.”